Make money doing the work you believe in
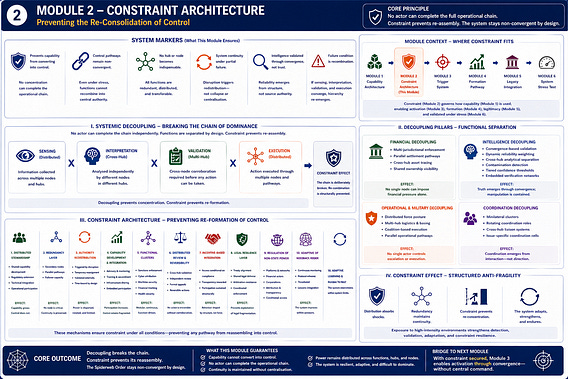
Module 2 — Constraint Architecture (Spiderweb Order)
How the Spiderweb Order prevents the re-consolidation of control
If the Spiderweb Order distributes capability, it must also prevent that capability from recombining into control.
This module defines the system’s constraint layer—how coordination remains possible while ensuring no actor, hub, or coalition can assemble end-to-end authority.
Constraint is not political. It is structural.
System Markers
Prevents capability from converting into control No concentration of power can complete the operational chain
Control pathways remain non-convergent Even under stress, functions cannot recombine into central authority
No hub becomes indispensable Functions are redundant, distributed, and transferable
System continuity under partial failure Disruption triggers redistribution—not collapse or centralisation
Intelligence is validated through convergence, not trust Reliability emerges from structure, not source
Failure condition is recombination If sensing, interpretation, validation, and action converge, hierarchy re-emerges
Capability development does not produce control pathways Expansion increases participation—but not coordination authority
System Layer
Constraint Architecture: Anti-Centralisation System
Position in Architecture
Constraint enforcement layer governing all capability use
Primary Function
To prevent recombination of control across sensing, validation, and action pathways—even as capability expands
Constraint Condition
No domain, hub, or coalition retains end-to-end control across any operational chain
Interaction with Other Modules
Module 1 — Capability Architecture
Module 3 — Trigger System
Module 4 — Formation Pathway
Module 5 — Legacy Integration
Module 6 — System Stress Test
Internal Structure — Decoupling and Constraint System
System Function — Structural Constraint Enforcement
The Spiderweb Order does not rely on political restraint or alignment to limit dominance.
Constraint is structural.
It is embedded in:
how information is produced and shared
how interpretation is formed
how validation occurs
how distributed action is executed
The system is not permissively decentralised—it is deliberately non-convergent.
Efficiency is traded for resilience. Speed is preserved through distribution—not centralisation.
Critical Extension — Constraint on Development
Constraint applies not only to existing capability—but to capability growth.
As capability diffuses:
participation increases
integration deepens
control pathways remain fragmented
Effect: Growth strengthens the system without enabling dominance
Mechanisms — Decoupling, Constraint, and Integrity Systems
I. Systemic Decoupling — Breaking the Control Chain
Traditional chain: detection → interpretation → decision → execution
Spiderweb separation:
detection is distributed
interpretation is cross-hub
validation is multi-hub
execution is distributed
No actor completes the chain independently.
A. Financial Decoupling
Objective: eliminate single-point financial dominance
Mechanisms:
multi-jurisdictional sanctions
parallel clearing pathways
cross-hub asset tracing
shared ownership visibility
Effect: Financial pressure becomes network-wide; arbitrage loses effectiveness
B. Intelligence Decoupling — Distributed Interpretation
Objective: maintain analytical integrity without central authority
The system assumes:
uneven intelligence quality
partial or manipulated inputs
variable hub capacity
high-frequency real-time inputs
The solution is structured reliability—not centralised trust.
1. Convergence-Based Validation
Requires:
cross-hub corroboration
multi-domain alignment
temporal consistency
High-intensity signals increase density—but not authority
Effect: Truth emerges through convergence
2. Dynamic Reliability Weighting
Nodes are weighted by:
historical accuracy
correlation with verified data
consistency
exposure to contradiction
Effect:
reliable inputs gain influence
distorted inputs are suppressed
density increases sensitivity without control
3. Cross-Hub Analytical Separation
collection in one hub
analysis in another
validation across others
Effect: prevents narrative shaping at source
4. Contamination Detection
Identifies:
anomalous reporting
coordinated distortion
hidden linkages
Effect: Manipulation becomes detectable signal
5. Tiered Confidence Thresholds
low → monitoring
medium → adjustment
high → distributed action
Effect: Adaptive response without premature escalation
6. Isolation Without Fragmentation
Compromised nodes are:
de-weighted
access-limited
supported through development pathways
Effect:
preserves cohesion
prevents exploitation
restores integrity
7. Embedded Verification Networks
rotating teams
cross-hub validation
no central authority
Effect: Verification without centralisation
Core Constraint — Intelligence Layer
No single intelligence stream—regardless of origin, volume, or credibility—can trigger system-wide action
C. Operational & Military Decoupling
Objective: prevent command concentration
Mechanisms:
distributed force posture
multi-hub logistics
coalition execution
parallel pathways
Capability informs coordination—but does not confer control
D. Coordination Decoupling
Objective: eliminate single-point coordination authority
Mechanisms:
minilateral clusters
rotating roles
liaison systems
issue-specific cells
Effect: Coordination emerges from interaction—not direction
II. Constraint Architecture — Preventing Re-Formation of Control
Decoupling prevents concentration. Constraint ensures it cannot reform.
A. Distributed Stewardship
Hubs support others through:
regulatory extension
technical integration
operational participation
Constraint:
capability diffuses
control does not
Effect:
capability expands
dependency decreases
dominance remains constrained
B. Secondary Hubs
backup hubs
parallel validation
failover execution
Effect: No hub becomes indispensable
C. Authority Redistribution Mechanism
Triggers:
disruption
overload
compromise
Process:
temporary reassignment
secondary activation
post-event validation
Constraint: Time-bound and externally validated
D. Capability Development & Integration
advisory systems
shared infrastructure
training and secondment
coordination integration
Constraint: Capability increases participation—not control
E. Minilateral Functional Clusters
sanctions
cyber attribution
maritime security
financial tracking
Design: modular, continuous, function-driven
F. Distributed Review & Reversibility
cross-hub validation
independent review
appeal pathways
Constraint: No action is irreversible without corroboration
G. Incentive-Based Integration
Access to:
markets
finance
intelligence
cooperation systems
is conditional on:
compliance
transparency
participation
Effect: Behaviour shaped structurally—not coercively
H. Legal Resilience Layer
treaty alignment
shared legal defence
arbitration resistance
coordinated enforcement
Effect: Prevents exploitation of fragmentation
I. Regulation of Non-State Power
Targets:
platforms
financial networks
corporations
Mechanisms:
transparency
cross-jurisdiction regulation
conditional access
attribution pathways
Effect: Private power remains constrained
J. Adaptive Learning & Feedback
continuous monitoring
protocol refinement
threshold recalibration
Effect: System improves under pressure
Critical Integration
Feedback loops reinforce constraint:
capability growth is evaluated
dominance risks are identified early
structure adapts to prevent consolidation
System Effect — Structured Anti-Fragility
The system achieves stability through:
distribution
redundancy
constrained interaction
As capability expands:
coordination redistributes
validation intensifies
constraint strengthens
Failure is absorbed—not cascaded
Core Strategic Outcome
The Spiderweb Order does not eliminate asymmetry. It prevents it from becoming decisive.
Power may accumulate— but it cannot assemble the full chain required for control.
The system does not require all actors to be reliable. It ensures no actor can unilaterally shape outcomes.
Micro-Reference
These constraints ensure capability defined in Module 1—and expanded through Module 4—cannot consolidate into control, and enable the distributed activation mechanisms in Module 3.