Make money doing the work you believe in
Module 3 — Trigger System (Spiderweb Order)
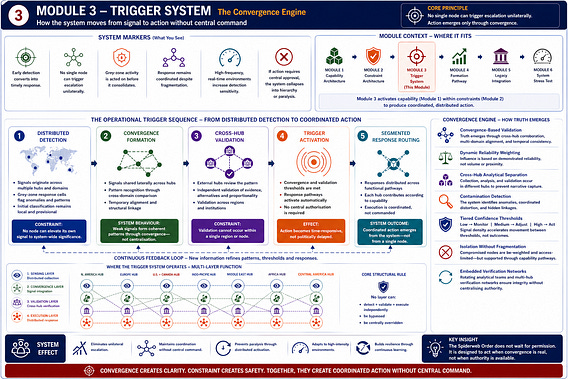
The Convergence Engine: How the system moves from signal to action without central command
If the Spiderweb Order distributes capability and constrains control, it must also define how action occurs.
This module explains how the system moves from signal to response—without central authority, unilateral escalation, or full-spectrum aggregation.
Action is not decided. It is triggered.
System Markers
What this module does: Transforms distributed signals into coordinated action without central authority
What changes: Action is triggered by convergence—not initiated by decision-makers
What success looks like:
early detection converts into timely response
no single node can trigger escalation
grey-zone activity is disrupted early
coordination persists despite fragmentation
high-frequency environments increase sensitivity without distorting control
Failure condition: If action requires central approval—or a single node can trigger escalation—the system collapses into hierarchy or paralysis
System Layer — Internal Mechanics
Trigger System: Convergence-Based Activation and Distributed Response
The Trigger System converts distributed sensing into coordinated action—without central command, unilateral authority, or full signal aggregation.
It operates under:
ambiguity
time pressure
contested attribution
high-frequency signal environments
A. Trigger Architecture — Convergence Over Authority
Action is not initiated by any hub, node, or source.
It emerges through convergence across three dimensions:
1. Multi-Domain Signal Detection
Signals emerge across:
cyber
financial
maritime and logistics
information environments
legal and institutional systems
Signal generation is uneven.
Some nodes operate in high-intensity environments, producing:
continuous real-time data
rapid operational feedback
high-volume signals under pressure
No domain is decisive. All signals remain partial until correlated.
2. Cross-Node Correlation
Signals are:
compared across hubs
assessed against shared standards
tested for pattern consistency:
persistence
repetition
cross-domain linkage
Correlation is horizontal—not centralised.
High-frequency environments increase:
pattern visibility
anomaly detection
temporal resolution
But do not determine interpretation.
3. Threshold-Based Convergence
A trigger condition is met when:
independent nodes detect aligned indicators
signals converge across domains
credibility thresholds are satisfied
High-density environments accelerate convergence—but cannot satisfy thresholds alone.
Result: Action becomes a function of convergence—not authority or signal volume
B. Validation Layer — Distributed Legitimacy
Once convergence is reached, validation precedes response.
Multi-Hub Validation
at least one external hub participates
independent verification pathways engage
disputes are resolved through evidence—not hierarchy
Segmentation of Validation Authority
no node validates itself
validation is externally dependent
Optional Oversight (Contested Cases)
Rotating or cross-hub bodies assess:
proportionality
evidentiary sufficiency
systemic risk
Outcome
Legitimacy emerges through convergence—not permission
C. Response Routing System — Segmented Execution
Responses are distributed—not centrally directed.
Response Pathways
Financial sanctions, asset restriction, system exclusion
Legal & Regulatory jurisdictional action, treaty enforcement
Cyber & Information attribution, countermeasures, platform response
Physical & Maritime monitoring, interdiction, access denial
Political Signalling attribution, diplomacy, narrative stabilisation
Each pathway:
is executed by different hubs
follows shared protocols
does not require full participation
High-intensity environments enhance speed and adaptation—but do not centralise control.
D. Response Ladder — Graduated Action
monitoring and adaptation
confidential engagement
public attribution
coordinated restrictions
sustained containment
Constraints
escalation is proportional
measures are reversible
actions are periodically reviewed
E. Temporal Compression — Acting Without Delay
Pre-Agreed Thresholds
shared definitions of grey-zone activity
standardised trigger conditions
pre-authorised response frameworks
Standing Operational Cells
Permanent multi-domain teams:
cyber
financial
maritime
information
network mapping
High-tempo nodes provide continuous updates—improving responsiveness without altering control.
Parallel Processing
detection
validation
response preparation
occur simultaneously
Outcome: Faster action without sacrificing legitimacy
F. Anti-Centralisation Safeguards
no full-spectrum intelligence fusion
no central authority
no unified command
no single escalation point
If a node is:
compromised → others continue
delayed → parallel pathways proceed
contested → additional validation engages
G. Failure Handling and Dispute Management
Disagreement is expected.
Disputes Over Facts
Resolved through:
additional data
joint investigation
expanded verification
Disputes Over Thresholds
managed through escalation ladders
allows partial participation
System Behaviour
action degrades in intensity—not existence
lower-tier responses proceed
H. Integration with System Architecture
The Trigger System connects to:
Module 1 → defines execution capability
Module 2 → enforces distributed validation
Module 4 → builds thresholds and protocols
Module 5 → provides post-action legitimacy
System Effect
The Trigger System enables:
coordinated action without command
rapid response without bottlenecks
legitimacy without dependency
escalation control without dominance
Core Transformation
Traditional Model: detection → decision → command → execution
Spiderweb Model: detection → convergence → validation → distributed action
Functional Layers
Sensing → distributed detection
Convergence → pattern formation
Validation → cross-hub verification
Execution → distributed response
Core Rule
No layer can: detect + validate + execute independently
Resilience Under Noise and Manipulation
The system operates under:
incomplete information
contested intelligence
adversarial interference
high-volume noise
It manages this through:
convergence thresholds
distributed validation
tiered responses
Effect:
false signals are absorbed
distorted inputs are diluted
persistent patterns gain weight
Strategic Effect — Early Action
By acting in the grey zone:
coercion is disrupted early
ambiguity is reduced
costs are imposed incrementally
High-frequency environments improve detection without forcing escalation.
Core Strategic Outcome
The system ensures:
action cannot be indefinitely delayed
escalation cannot be unilateral
coordination persists under pressure
Closing
The Spiderweb Order does not wait for certainty—nor allow unconstrained action.
It moves when patterns converge.
Response is neither paralysed by doubt nor captured by any single actor.
The Trigger System operationalises the architecture—converting distributed signals into coordinated action.