The app for independent voices
Preparing for Security+, CC, or CISSP?
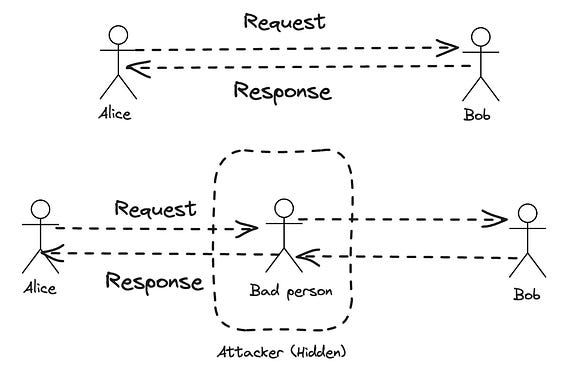
Then you need to understand Man-in-the-Middle attacks.
Not the definition.
👉 How they actually work
👉 Where they happen in the communication flow
👉 Why they succeed
Because exam questions won’t ask you: “What is MitM?”
They’ll ask: “Where does the attack break trust?”
That’s a completely different level.
Apr 12
at
1:10 PM
Relevant people
Log in or sign up
Join the most interesting and insightful discussions.
