Make money doing the work you believe in
Distributed Log Implementation With Java & Spring Boot
What We’re Building Today
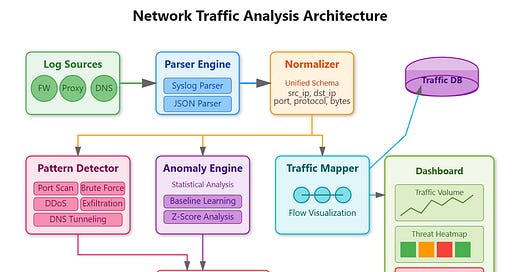
You’ll implement a real-time network security monitoring system that analyzes log data to detect threats, map traffic patterns, and identify anomalies. Think of how Cloudflare monitors billions of requests to block DDoS attacks, or how Netflix tracks traffic patterns to detect account sharing—we’re building that intelligence layer.
Today’s Goals:
Parse network logs (firewall, proxy, packet captures) in real-time
Detect suspicious patterns (port scans, data exfiltration, brute force)
Visualize traffic flows with threat scoring
Generate actionable security alerts
May 6
at
11:20 AM
Relevant people
Log in or sign up
Join the most interesting and insightful discussions.