The app for independent voices
𝗛𝗼𝘄 𝗱𝗼𝗲𝘀 𝗔𝗽𝗽𝗹𝗲 𝗳𝗶𝗻𝗱 𝘆𝗼𝘂𝗿 𝗹𝗼𝘀𝘁 𝗔𝗶𝗿𝗧𝗮𝗴 𝗶𝗻 𝘁𝗵𝗲 𝗺𝗶𝗱𝗱𝗹𝗲 𝗼𝗳 𝗻𝗼𝘄𝗵𝗲𝗿𝗲?
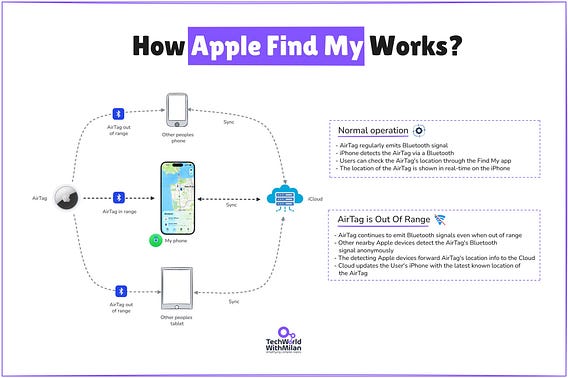
No GPS. No cellular. No WiFi. Just math and a billion devices working together.
𝗧𝗵𝗲 𝗕𝗮𝘀𝗶𝗰𝘀
Your AirTag broadcasts a Bluetooth signal every few seconds. But it broadcasts a 𝗽𝘂𝗯𝗹𝗶𝗰 𝗸𝗲𝘆, not an identifier.
Any nearby iPhone that picks up this signal grabs its own GPS location, encrypts it with the AirTag's public key, and uploads it to Apple's servers.
The owner downloads these encrypted reports and decrypts them locally. Apple never sees the location.
𝗧𝗵𝗲 𝗖𝗿𝘆𝗽𝘁𝗼𝗴𝗿𝗮𝗽𝗵𝘆
Apple uses P-224 elliptic curve cryptography. The public key rotates every 15 minutes.
A Johns Hopkins cryptographer put it well: even if someone tracked your device's signals all day, they "wouldn't be able to recognize you were the same person from one hour to the next."
𝗧𝗵𝗲 𝗦𝗰𝗮𝗹𝗲 𝗘𝗻𝗴𝗶𝗻𝗲𝗲𝗿𝗶𝗻𝗴
Apple turned 1+ billion devices into a global mesh of location relays. Every iPhone running iOS 13+ becomes infrastructure. No new hardware. No subscriptions.
On the backend:
🔹 Reports indexed by 𝗵𝗮𝘀𝗵𝗲𝗱 public keys. Apple can't link them to owners
🔹 Only the 𝗹𝗮𝘁𝗲𝘀𝘁 location is stored, caps data volume
🔹 All decryption happens on-device, not Apple's servers
One clever constraint: you need two Apple devices on your account. One decrypts the other's location. Always a key holder available.
Crypto techniques have existed in academia for years. Apple was first to deploy them at a billion-device scale, with end-to-end encryption, crowdsourced infrastructure, and rotating keys that prevent tracking.
This is what good system design looks like. Solving a hard distributed systems problem by making a billion devices work together, without any of them knowing what they're doing.