The app for independent voices
𝗪𝗵𝗶𝗰𝗵 𝗥𝗘𝗦𝗧 𝗔𝗣𝗜 𝗔𝘂𝘁𝗵𝗲𝗻𝘁𝗶𝗰𝗮𝘁𝗶𝗼𝗻 𝗠𝗲𝘁𝗵𝗼𝗱 𝗦𝗵𝗼𝘂𝗹𝗱 𝗬𝗼𝘂 𝗨𝘀𝗲?
Not all authentication methods are created equal. Therefore, an improper choice could leave your API unsecured or make your architecture overly complicated.
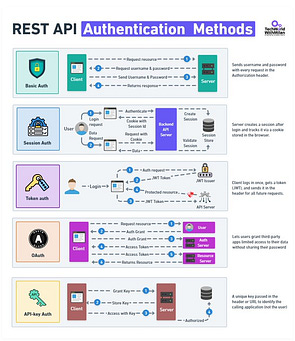
Here are 𝟱 𝗮𝘂𝘁𝗵𝗲𝗻𝘁𝗶𝗰𝗮𝘁𝗶𝗼𝗻 𝗺𝗲𝘁𝗵𝗼𝗱𝘀 and when to use each:
𝟭. 𝗕𝗮𝘀𝗶𝗰 𝗔𝘂𝘁𝗵
Sends username and password in each and every request in the 𝗔𝘂𝘁𝗵𝗼𝗿𝗶𝘇𝗮𝘁𝗶𝗼𝗻 header. Easy to implement, but sends credentials with every request. To be used only when deployed over 𝗛𝗧𝗧𝗣𝗦 and for internal usage only.
𝟮. 𝗦𝗲𝘀𝘀𝗶𝗼𝗻 𝗔𝘂𝘁𝗵
The server establishes a session after authentication and tracks it by sending a 𝗰𝗼𝗼𝗸𝗶𝗲 to the client's browser. For web applications where both frontend and backend are deployed at the same origin, this is an acceptable choice. For mobile and microservices architectures, sessions are not recommended because they do not scale horizontally.
𝟯. 𝗧𝗼𝗸𝗲𝗻 𝗔𝘂𝘁𝗵 (𝗝𝗪𝗧)
The user logs in once and receives a 𝗝𝗦𝗢𝗡 𝗪𝗲𝗯 𝗧𝗼𝗸𝗲𝗻. The user sends this token in the header for all subsequent requests. The system is stateless and scalable. The server does not have to store sessions. This is the go-to authentication mechanism for modern APIs and SPAs.
However, be careful about token expiration. The standard practice is to use short-lived tokens with a refresh token.
𝟰. 𝗢𝗔𝘂𝘁𝗵 𝟮.𝟬
This authentication mechanism allows users to grant third-party applications limited access to their data without sharing their passwords. The process involves authorization grants and access tokens between multiple parties. This authentication mechanism is used when you want to provide delegated access.
Think of "Login with Google" or third-party applications accessing your API.
𝟱. 𝗔𝗣𝗜 𝗞𝗲𝘆 𝗔𝘂𝘁𝗵
In this mechanism, a unique key is passed as a header or as a URL parameter to identify the 𝗰𝗮𝗹𝗹𝗶𝗻𝗴 𝗮𝗽𝗽𝗹𝗶𝗰𝗮𝘁𝗶𝗼𝗻. This is a good mechanism for server-to-server communication and for client rate limiting.
However, avoid using this mechanism as the primary user authentication method, since an API key is not a user representation.
Quick rule: JWT for most APIs. OAuth when third parties need access. API keys for service identification. Session auth for traditional web apps. Basic auth only when nothing else works.
What authentication mechanism are you using for your current project?